I just got back from a trip to sunny Southern California where I was staying just a few blocks away from the magic of Disneyland at an Air BnB.
That’s where I met Doug Kroll, a chiropractor from Hawaii and naturally, because I am a huge SEO nerd, we started talking about websites. He told me about his property management site and how it needed some work, so I started poking around looking at his site.

The Power Of the Site: Query
Since the first few steps that I always take on my site audits is to see what Google knows about a site I ran a site:http://url query. (Just type site: and then your full url) This lets me see fairly quickly if all the pages are properly getting indexed.
Doug’s Lexington rental property site had just 7 total pages. So when Google showed me this, my heart leapt into my throat.
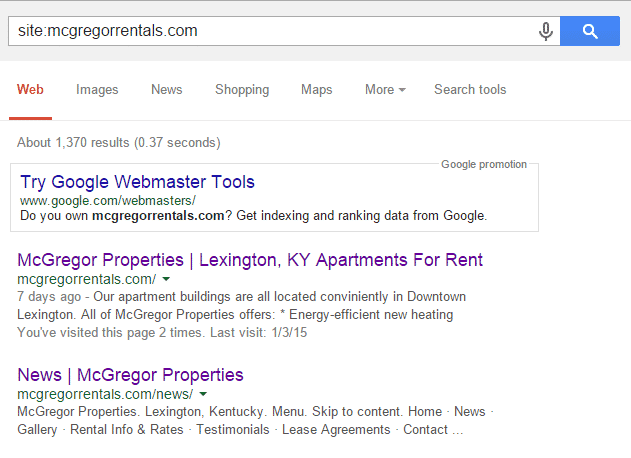
While those first few pages look fine, there’s just 7 URLs. Is there some weird tag issue going on here? I click to page 4.
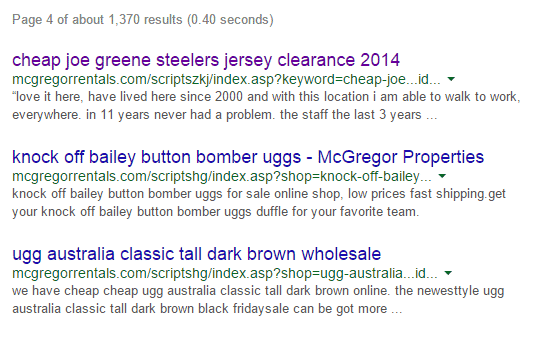
Uh oh. Mission control, we have a problem.
It’s Offical: The Site Has Been Hacked
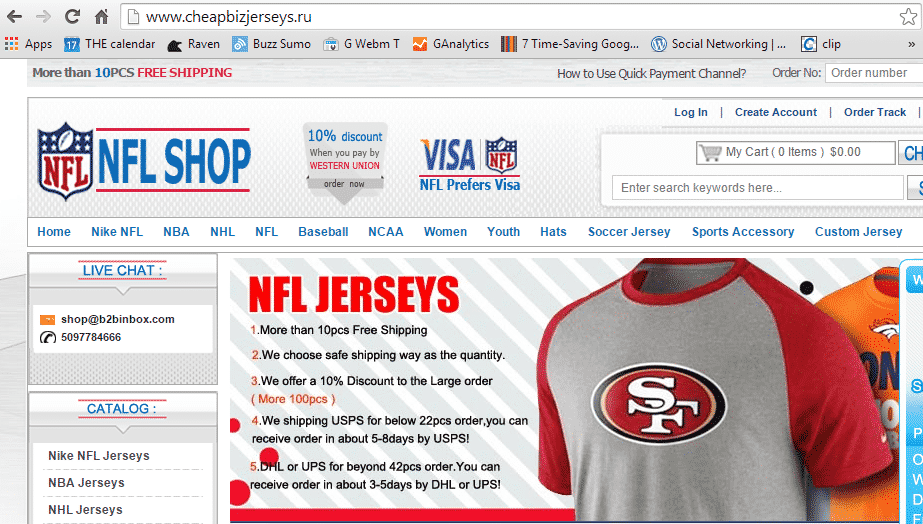
I did a couple Google searches around the domains being referenced and redirected. I found several articles about WordPress script inject and htaccess redirect hacks. Bingo. That just about fits the bill.
Digging Deeper
Once I told Doug about the problem, I had him update all his credentials and run an antivirus scan on his laptop. Then my second step was to login to Google Webmaster Tools, once Doug gave me access as a user.
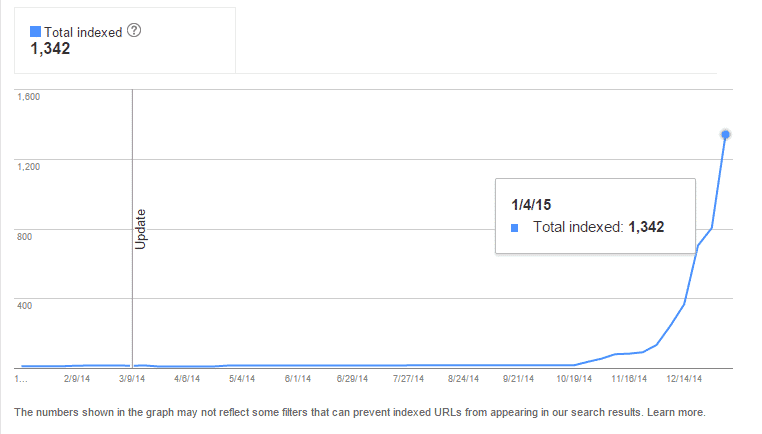
It looks like around 10/24 the hack occured based on the increasing amountof those bad URLs were being indexed from that date onward.
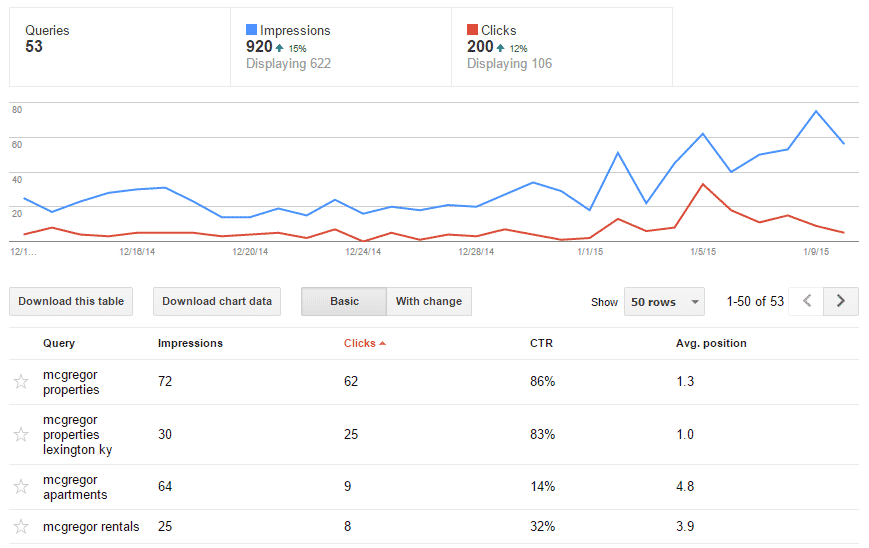
However, it looks like Google has not yet sent any messages, added a malware warning or penalized the site’s indexation, ranking, or traffic for their brand.
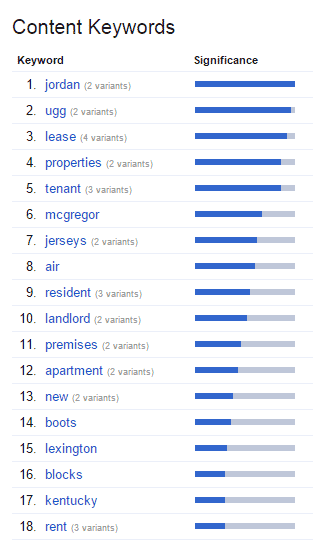
Well, Google definitely is seeing the spam content keywords, so that’s not good. Isn’t it interesting that this level of spam injected into a site is not causing a penalty, at least not an obvious one yet?
Let’s Clean This Up!
Since the injection involved the HTACCESS file, and the site was so small I suggested to Doug that we just scrap the whole site instead of try to dig out all of the bad files. With his consent, I called up the hosting company and killed it with fire and started a brand new WordPress site on a fresh server.
That’s about where I am in the process. I got permission from Doug to post about the hack, and thought I’d put out an open line for suggestions since the next step is dealing with the aftermath. Here’s my first thougts on next steps:
- Already had client update his email UN/PW, Hosting UN/PW and run a malware check and antivirus scan on his laptop.
- Add a 410 for the /script/ urls.
- Mark those now 500 Errors in Google Webmaster tools as fixed.
- Add in an extra WordPress security plugin – (Thinking about Securi).
What do you think? Have you dealt with a hacked site of your own or for a client recently? What would you do next?